Structure & traceability
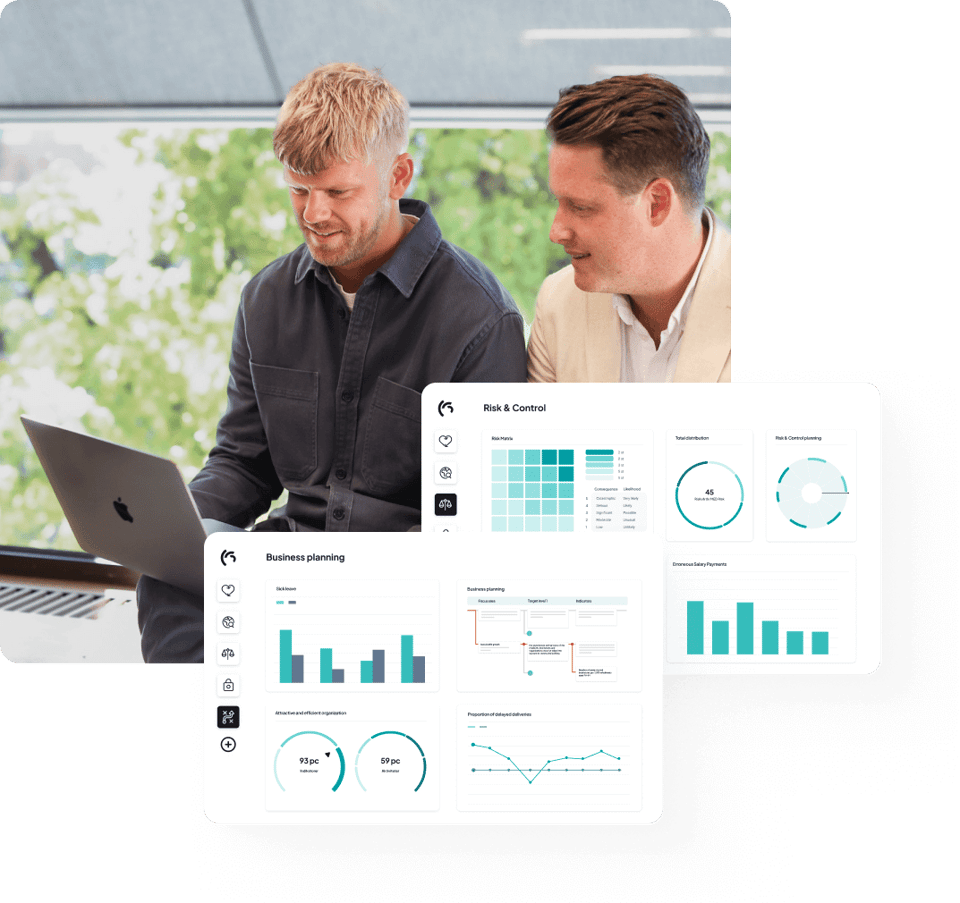
Create a clear structure for risk analyses, actions, and responsibilities. All documentation is gathered centrally and becomes traceable for audits or inspections.
NIS2 & The Cybersecurity Act
The NIS2 Directive and the Cybersecurity Act introduce stricter requirements for governance, follow-up, and accountability. With Stratsys, you get effective support to ensure compliance and strengthen your organization’s resilience.


Create a clear structure for risk analyses, actions, and responsibilities. All documentation is gathered centrally and becomes traceable for audits or inspections.
Coordinate the work in a shared system that automates processes and reduces duplicate efforts.
Gain a comprehensive overview of risks and actions. Strengthen decision-making with real-time data and act more proactively.
Mapping & risk management
Create a fact-based picture of your organization’s risk exposure. With a clear structure, you can identify critical vulnerabilities and obtain decision support that makes it easier to prioritize the right actions.

Implementation & third-party risks
Translate requirements and decisions into clear controls and routines, both internally and throughout the supplier chain. Reduce third-party risks and ensure that the entire chain operates in line with your security requirements.

Continuity & incident management
Ensure continuity in critical processes and create a structured way to follow up on incidents, link them to risks, and extract insights that strengthen the organization.

Follow-up & improvement
Get a comprehensive overview of compliance, risk management, and actions, and track how your security work evolves over time.

We chose Stratsys because it’s a unified and user-friendly platform. It helps us bring together key areas such as information security, data protection, continuity, and supplier management in a clear and structured way.


Customers
Users
Customers stay with us year after year

Ready to take the next step?
Discover how you can centralize, structure, and follow up on your entire security work in a system that provides clarity and confidence.
With over 25 years of experience, Stratsys offers a platform that simplifies the management of regulatory requirements in business-critical areas. Stratsys supports all governance processes and provides you with a platform that grows with you. Start where the need is greatest and scale up as your organization evolves.
NIS2 is an EU directive aimed at strengthening cybersecurity across the Union and protecting essential infrastructure from digital threats. In Sweden, NIS2 will form the basis for the new Cybersecurity Act (CSL), which introduces clearer and more extensive requirements for how organizations manage their security work—particularly in areas such as risk management, incident reporting, and accountability.
Both public and private entities that operate essential or important services will be covered. This includes organizations in sectors such as energy, transport, healthcare, finance, digital infrastructure, food supply, and waste management—along with several other critical areas.
The ultimate responsibility for NIS2 compliance lies with the organization’s executive management. This means that leadership is both legally and strategically accountable for ensuring that the organization meets the requirements—from establishing security measures to reporting incidents. As a result, cybersecurity becomes a management issue, not just an IT concern.
In Sweden, the new Cybersecurity Act is expected to come into force no earlier than 2025. During the transition period, the current NIS law remains in effect but should be interpreted in light of the NIS2 Directive. This means that companies should start preparing for the new requirements, even though they are not yet fully implemented.
Failure to comply may result in administrative fines, legal consequences, and damage to both your brand and operations. But it’s not just about avoiding penalties—it’s about building a robust security framework that reduces vulnerabilities and strengthens trust.

Many organisations have a clear view of which requirements apply and what needs to be developed within parts of information security. But the...

Supplier monitoring under NIS2 has become a central part of how organisations manage cybersecurity. As business-critical functions, systems and data...

How well does governance hold up when requirements tighten? With NIS2, information security is moving higher up the leadership agenda. For many...